CaptureBAT
Description
Capture client is a high interaction client honeypot which monitors the state of a system. It monitors processes, files, as well as the registry and classifies an event as being malicious by checking exclusion lists. These exclusion lists are regular expressions which can either allow or deny a particular event from a process in the system. Because of the fact that it uses regular expressions, creating these lists can be very simple but can also provide very fine grained exclusions if needed. The client can also copy all modified and deleted files to a temporary directory as well as capture all incoming and outgoing packets on the network adapters.
The client can be run in the following two modes:
- Client<->Server
- The client connects to a central Capture server that provides the client with URLs to visit, along with the browser to use, and the time of the navigation. While the URL is being visited the state of the system is monitored and if anything malicious occurs during the browsing period, the event is passed back to the server. In this mode the client is run inside of a virtual machine so that when a malicious event occurs, the server can revert the virtual machine to a clean state.
- To use this mode the options -s, -a and -b must be set so the client knows how to connect and authenticate with the server. To configure the programs that are available to visit a URL, edit the clients.conf file. If -cn are set then the log directory will be sent to the server once a malicious URL is visited. For this to work tar.exe and gzip.exe must be included in the Capture Client folder.
- Standalone
- In this mode the client runs in the background of a system and monitors the state of it. Rather than being controlled by a remote server, the user has control over the system. Malicious events can either be stored in a file or outputted to stdout.
Installation
CaptureBAT is available here (MD5: c1894e46ffe89be6ca35729d9dab6145):
- Link 1: https://www.honeynet.org/files/CaptureBAT-Setup-2.0.0-5574.exe
- Link 2: http://zeltser.com/reverse-malware/CaptureBAT-Setup-2.0.0-5574.exe
Usage
Syntax
Usage: CaptureBAT.exe [-chn] [-s server_ip -a vm server_id -b vm_id] [-l file]
Options
- -h
- Print this help message
- -s ip
- IP address of the server the client connects to. NOTE -a and -b must be defined when using this option
- -a server_id
- Unique id of the virtual machine server that hosts the client
- -b vm_id
- Unique id of the virtual machine that this client is run on
- -l file
- Output system events to a file rather than stdout
- -c
- Copy files into the log directory when they are modified or deleted
- -n
- Capture all incoming and outgoing network packets from the network adapters on the system and store them in .pcap files in the log directory
Example
stdout
Start CaptureBAT prior to the execution of the malware. The stdout shows all files, processes and registry modifications:
C:\Program Files\Capture>CaptureBAT.exe -c
Option: Collecting modified files
Driver already loaded: CaptureProcessMonitor
Driver already loaded: CaptureRegistryMonitor
Loaded filter driver: CaptureFileMonitor
---------------------------------------------------------
process: created C:\WINDOWS\explorer.exe -> C:\malware\443.exe
file: Delete C:\malware\443.exe -> C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\__tmp_rar_sfx_access_check_260234
file: Write C:\malware\443.exe -> C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmartMax.dll
file: Write C:\malware\443.exe -> C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.dat
file: Write C:\malware\443.exe -> C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.dat
file: Write C:\malware\443.exe -> C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.exe
file: Write C:\malware\443.exe -> C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.exe
registry: SetValueKey C:\malware\443.exe -> HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders\Personal
registry: SetValueKey C:\malware\443.exe -> HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\{676f8e32-e1b0-11e2-9cdf-806d6172696f}\BaseClass
registry: SetValueKey C:\malware\443.exe -> HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\{676f8e30-e1b0-11e2-9cdf-806d6172696f}\BaseClass
registry: SetValueKey C:\malware\443.exe -> HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders\Common Documents
registry: SetValueKey C:\malware\443.exe -> HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders\Desktop
registry: SetValueKey C:\malware\443.exe -> HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders\Common Desktop
registry: SetValueKey C:\malware\443.exe -> HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\ProxyBypass
registry: SetValueKey C:\malware\443.exe -> HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\IntranetName
registry: SetValueKey C:\malware\443.exe -> HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\UNCAsIntranet
registry: SetValueKey C:\malware\443.exe -> HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\AutoDetect
registry: SetValueKey C:\malware\443.exe -> HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\ProxyBypass
registry: SetValueKey C:\malware\443.exe -> HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\IntranetName
registry: SetValueKey C:\malware\443.exe -> HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\UNCAsIntranet
registry: SetValueKey C:\malware\443.exe -> HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\AutoDetect
registry: SetValueKey C:\malware\443.exe -> HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders\Cache
registry: SetValueKey C:\malware\443.exe -> HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders\Cookies
process: created C:\malware\443.exe -> C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.exe
file: Write C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.exe -> C:\Program Files\Capture\logs\deleted_files\C\malware\443.exe
file: Write C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.exe -> C:\Program Files\Capture\logs\deleted_files\C\malware\443.exe
file: Write C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.exe -> C:\Program Files\Capture\logs\deleted_files\C\malware\443.exe
file: Write C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.exe -> C:\Program Files\Capture\logs\deleted_files\C\malware\443.exe
file: Delete C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.exe -> C:\malware\443.exe
process: terminated C:\WINDOWS\explorer.exe -> C:\malware\443.exe
file: Delete C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.exe -> C:\malware\443.exe
file: Write C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.exe -> C:\Documents and Settings\All Users\SxSx\NvSmart.dat
process: created C:\WINDOWS\system32\svchost.exe -> C:\WINDOWS\system32\wbem\wmiprvse.exe
file: Write C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.exe -> C:\Documents and Settings\All Users\SxSx\NvSmart.exe
file: Write C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.exe -> C:\Documents and Settings\All Users\SxSx\NvSmartMax.dll
registry: SetValueKey C:\Program Files\IETab\IETab.exe -> HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\IETab
process: created C:\WINDOWS\system32\wbem\wmiprvse.exe -> C:\Documents and Settings\All Users\SxSx\NvSmart.exe
file: Write System -> C:\Program Files\Capture\logs\deleted_files\C\malware\443.exe
file: Write System -> C:\Program Files\Capture\logs\deleted_files\C\malware\443.exe
process: created C:\WINDOWS\system32\services.exe -> C:\Documents and Settings\All Users\SxSx\NvSmart.exe
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system.LOG
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\system32\config\system
process: created C:\Documents and Settings\All Users\SxSx\NvSmart.exe -> C:\WINDOWS\system32\svchost.exe
process: terminated C:\WINDOWS\system32\services.exe -> C:\Documents and Settings\All Users\SxSx\NvSmart.exe
process: terminated C:\malware\443.exe -> C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.exe
process: terminated C:\WINDOWS\system32\wbem\wmiprvse.exe -> C:\Documents and Settings\All Users\SxSx\NvSmart.exe
registry: SetValueKey C:\WINDOWS\system32\svchost.exe -> HKLM\SOFTWARE\Classes\FAST\CLSID
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\Debug\UserMode\userenv.log
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\Debug\UserMode\userenv.log
file: Write C:\WINDOWS\system32\services.exe -> C:\WINDOWS\Debug\UserMode\userenv.log
file: Write C:\Documents and Settings\All Users\SxSx\NvSmart.exe -> C:\Documents and Settings\All Users\SxS\bug.log
file: Write C:\Documents and Settings\All Users\SxSx\NvSmart.exe -> C:\Documents and Settings\All Users\SxS\bug.log
file: Write C:\Documents and Settings\All Users\SxSx\NvSmart.exe -> C:\Documents and Settings\All Users\SxS\bug.log
file: Write C:\Documents and Settings\All Users\SxSx\NvSmart.exe -> C:\Program Files\Capture\logs\deleted_files\C\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.exe
file: Delete C:\Documents and Settings\All Users\SxSx\NvSmart.exe -> C:\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.exe
file: Write C:\WINDOWS\system32\svchost.exe -> C:\Documents and Settings\LocalService\IETldCache\index.dat
file: Write C:\WINDOWS\system32\svchost.exe -> C:\Documents and Settings\All Users\SxS\bug.log
file: Write C:\WINDOWS\system32\svchost.exe -> C:\Documents and Settings\All Users\SxS\bug.log
file: Write C:\WINDOWS\system32\svchost.exe -> C:\Documents and Settings\All Users\SxS\bug.log
file: Write System -> C:\Program Files\Capture\logs\deleted_files\C\malware\443.exe
file: Write System -> C:\Program Files\Capture\logs\deleted_files\C\malware\443.exe
file: Write System -> C:\Program Files\Capture\logs\deleted_files\C\Documents and Settings\unknown\Local Settings\Temp\RarSFX0\NvSmart.exe
process: created C:\WINDOWS\system32\svchost.exe -> C:\WINDOWS\system32\msiexec.exe
file: Write C:\WINDOWS\system32\svchost.exe -> C:\Documents and Settings\All Users\SxS\bug.log
file: Write C:\WINDOWS\system32\svchost.exe -> C:\Documents and Settings\All Users\SxS\bug.log
file: Write C:\WINDOWS\system32\svchost.exe -> C:\Documents and Settings\All Users\SxS\bug.log
file: Write C:\WINDOWS\system32\svchost.exe -> C:\malware\practicalmalwareanalysis.log
file: Write C:\WINDOWS\system32\svchost.exe -> C:\malware\practicalmalwareanalysis.log
file: Write C:\WINDOWS\system32\svchost.exe -> C:\malware\practicalmalwareanalysis.log
file: Write C:\WINDOWS\system32\svchost.exe -> C:\malware\practicalmalwareanalysis.log
file: Write C:\WINDOWS\system32\svchost.exe -> C:\malware\practicalmalwareanalysis.log
^C
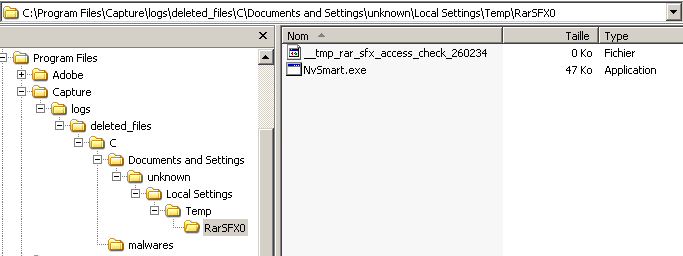
Logs
A log directory is created under the installation directory, showing deleted files: