Category:Digital-Forensics/Computer-Forensics/Anti-Reverse-Engineering/Anti-Disassembly/Jmp-Constant-Condition
| You are here | Jump instruction with constant condition
|
Description
| Byte code |
┌────┬────┬────┬────┬────┬────┬────┬────┬────┐ │ 33 │ C0 │ 74 │ 01 │ E9 │ 58 │ C3 │ 68 │ 94 │ └────┴────┴────┴────┴────┴────┴────┴────┴────┘ |
|
|---|---|---|
| Wrong interpretation |
┌─────────┬─────────┬────────────────────────┐ │XOR │JZ │JMP ... │ └─────────┴─────────┴────────────────────────┘ |
33 C0 xor eax, eax
74 01 jz short near ptr loc_4011C4+1
loc_4011C4: ; CODE XREF: 004011C2j
; DATA XREF: .rdata:004020AC0
E9 58 C3 68 94 jmp near ptr 90D0D521h
|
| Good interpretation |
┌─────────┬─────────┬────┬────┬────┬─────────┐
│XOR │JZ │ │POP │RET │ │
└─────────┴─────────┴────┴────┴────┴─────────┘
│ ▲
└────────────┘
|
33 C0 xor eax, eax
74 01 jz short near ptr loc_4011C5
; -------------------------------------------------------------------
E8 db 0E9h
; -------------------------------------------------------------------
loc_4011C5: ; CODE XREF: 004011C2j
; DATA XREF: .rdata:004020AC0
58 pop eax
C3 retn
|
Example
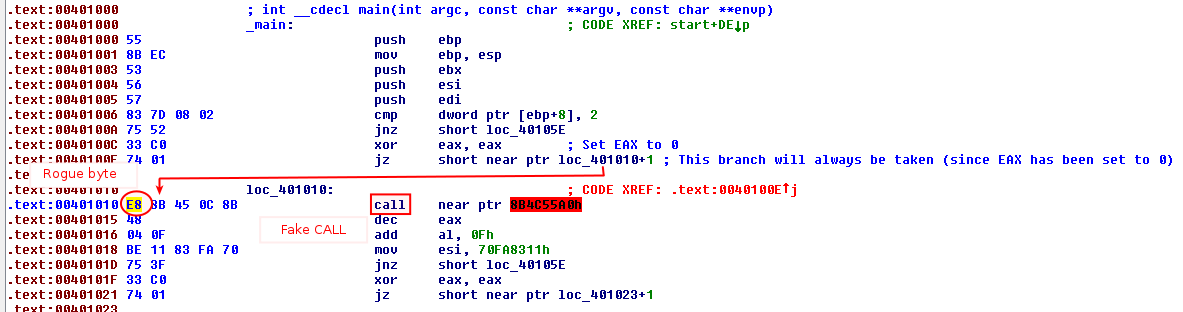
Below is an example of this technique:
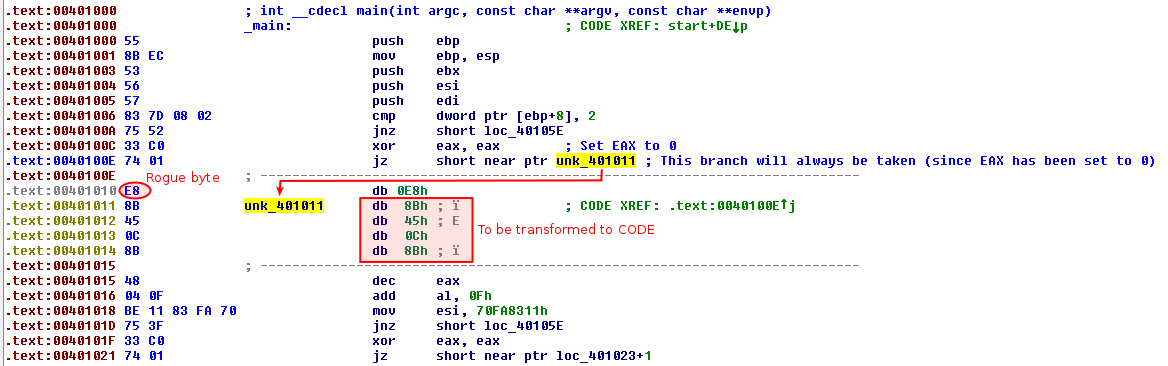
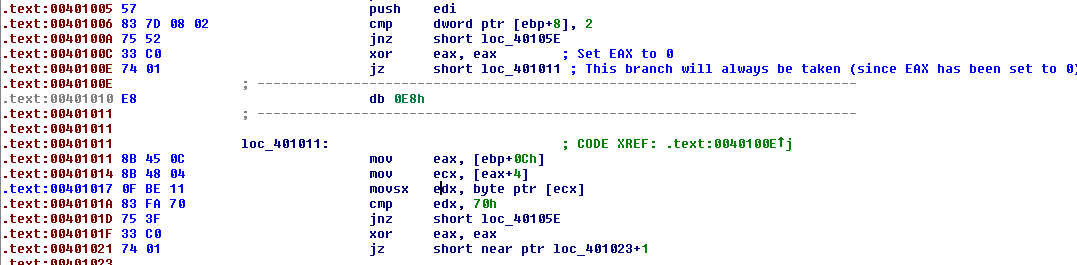
Notice that the conditional jump (jz) at 0x40100E is actually unconditional since EAX is set to 0 just one instruction before (xor eax, eax at offset 0x40100C). It jumps to the middle of the 5-byte fake CALL. Let's adjust this in IDA-Pro. Place your cursor at the offset 0x401010 and press D to transform the block to DATA. Here is what it results in:
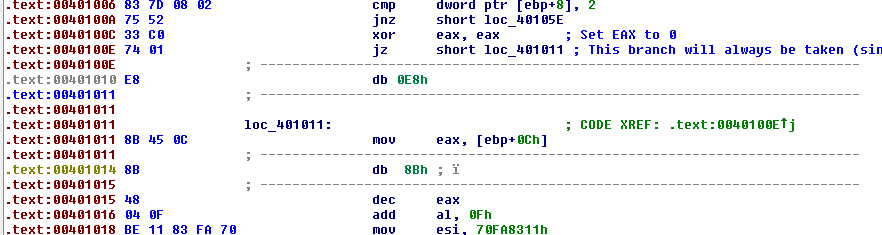
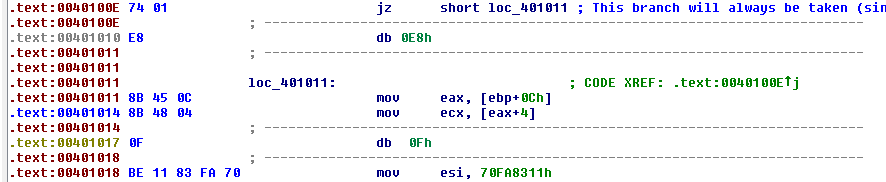
Now, let's convert the block from 0x401011 back to CODE by pressing C. You will need to do it several times:
|

|
|

|
|
Once all modifications have been done, you still need to tell IDA-Pro that this block of code is a function. To do that, select the entire function code, from the beginning of the function till the return instruction and press P.
Pages in category "Digital-Forensics/Computer-Forensics/Anti-Reverse-Engineering/Anti-Disassembly/Jmp-Constant-Condition"
This category contains only the following page.