Dns2tcp
Description
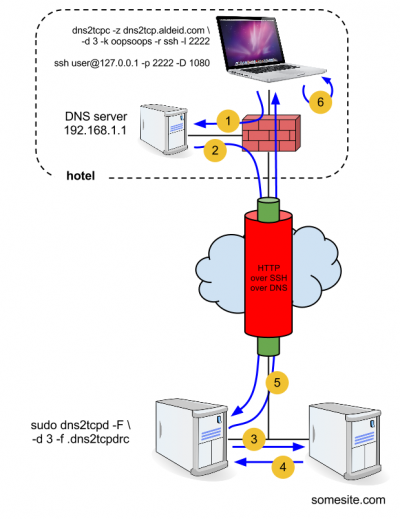
Dns2tcp is a tool for relaying TCP connections over DNS. Among other things, it can be used to bypass captive portals (e.g. hotels, airport, ...) when only port 53/udp is allowed by the firewall. Here is how we are going to use it:
|
Prerequisites
Prior to what follows, you will need:
- a domain name (e.g. aldeid.com)
- a NS record (e.g. dns2tcp) on your domain name that points to the public name of your dns2tcp public server (you can achieve this using no-ip.org).
Here is an example:
dns2tcp IN NS aldeid.no-ip.org.
with aldeid.no-ip.org being the name of the dns2tcp public server.
Installation
From sources
It will install the latest version available at the time of this writing: v0.5.2. I have successfully compiled dns2tcp from sources on Ubuntu Server 11.04 32bits and Mac OS X 10.7.
$ cd /usr/local/src/ $ wget http://hsc.fr/ressources/outils/dns2tcp/download/dns2tcp-0.5.2.tar.gz $ tar xzvf dns2tcp-0.5.2.tar.gz $ cd dns2tcp-0.5.2/ $ ./configure $ make $ sudo make install
apt linux packages
It will install version 0.5.1.
$ sudo apt-get install dns2tcp
macports
It will install version 0.4.
$ sudo port install dns2tcp
Usage
Server
Options
- -h
- Help Menu
- -F
- Run in foreground
- -i <IP address>
- IP address to bind (default 0.0.0.0)
- -f <config file>
- Configuration file to use
- -p <pidfile>
- File where our pid will be written
- -d <debug level>
- Change debug level. Levels available are 1, 2 or 3.
Configuration
Create a configuration file in your home directory as follows:
$ cat ~/.dns2tcpdrc listen = 88.192.45.134 port = 53 user=nobody chroot = /var/empty/dns2tcp/ pid_file = /var/run/dns2tcp.pid domain = dns2tcp.aldeid.com key = oopsoops resources = ssh:127.0.0.1:22
Start dns2tcpd
To test that the server works fine:
$ sudo dns2tcpd -F -d 3 -f ~/.dns2tcpdrc 15:14:57 : Debug options.c:97 Add resource ssh:127.0.0.1 port 22 15:14:57 : Debug socket.c:55 Listening on 88.192.45.134:53 for domain dns2tcp.aldeid.com Starting Server v0.5.2... 15:14:57 : Debug main.c:132 Chroot to /var/empty/dns2tcp/ 13:14:57 : Debug main.c:142 Change to user nobody
To start the dns2tcpd server as a daemon:
$ sudo dns2tcpd -d 1 -f ~/.dns2tcpdrc
Client
Options
Syntax: dns2tcpc -z <dns2tcp_server> [options] [server]
- -h
- Help Menu
- -c
- Enable DNS compression. When used, be sure that all relay and DNS server support compression and really use it.
- -z <domain zone>
- Use this domain as endpoint.
- -d <debug level>
- Change debug level. Levels available are 1, 2 or 3.
- -r <resource>
- Remote resource to access.
- -k <key>
- Pre shared key used for authentication (identification).
- -f <config file>
- Configuration file to use.
- -T <request type>
- Request type to use. Actually only KEY and TXT requests are supported.
- -e <command>
- Command to execute, I/O are redirected in the tunnel.
- -l <local_port>
- Local port accepting incomming connections (or - for stdin on UNIX systems).
- -t <connection timeout>
- Maximum DNS server's answer delay in seconds. A valid delay is between 1 and 240 seconds. Default is 3.
- server
- DNS server to use. The first entry in resolv.conf file will be choosen if the server is not specified.
Configuration
Create a .dns2tcprc in your home directory as follows:
$ cat ~/.dns2tcprc domain = dns2tcp.aldeid.com resource = ssh local_port = 2222 key = oopsoops debug_level=3 # server = my_dns
Start dns2tcpc
First check available resources:
$ dns2tcpc -z dns2tcp.aldeid.com -d 3 -k oopsoops
No DNS given, using 192.168.1.254 (first entry found in resolv.conf)
debug level 3
Debug socket.c:233 Create socket for dns : '192.168.1.1'
Debug session.c:46 Request challenge
Debug requests.c:146 Sending dns id = 0x7238
Debug requests.c:95 Query is AAAAAKTfAA.=auth.tunnel.aldeid.com len 34
Debug rr.c:106 rr_decode_next_reply_encode base64 data was = IggAAKTfAFNXMDBFOTBOS045RUQwUk8 (reply len = 34)
Debug session.c:53 Challenge = 'SW00E90NKN9ED0RO'
17:14:10 : Debug session.c:54 Session created (0x822)
Debug session.c:77 Sending response : 'A88484E228BCCA3330705E2B20ADEBC33A0292FD' (key = PlRtSpA#123)
Debug requests.c:146 Sending dns id = 0xa40
Debug requests.c:95 Query is IgiBgAABAEE4ODQ4NEUyMjhCQ0NBMzMzMDcwNUUyQjIwQURFQkMzM0EwMjkyRkQ.=auth.tunnel.aldeid.com len 87
Debug rr.c:106 rr_decode_next_reply_encode base64 data was = IgiBgAABAA (reply len = 13)
17:14:10 : Debug auth.c:58 Requesting resource
Debug requests.c:146 Sending dns id = 0x1d26
Debug requests.c:95 Query is IghVV2GiAA.=resource.tunnel.aldeid.com len 38
Available connection(s) :
Debug rr.c:106 rr_decode_next_reply_encode base64 data was = e7eduWO3AHNzaA (reply len = 17)
ssh
Note : Compression SEEMS available !
Select a resource and open a connection as follows:
$ dns2tcpc -z dns2tcp.aldeid.com -k oopsoops -r ssh -l 2222 Listening on port : 2222
Now ensure the connection will be encrypted:
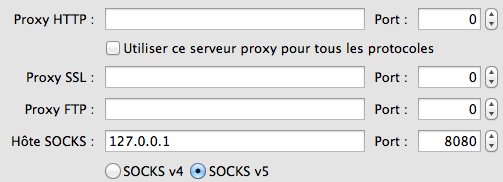
$ ssh [email protected] -p 2222 -D 8080
The above command will create a SOCKS5 proxy that we will use to configure our browser: