Pin
Description
Pin is a dynamic binary instrumentation framework for the IA-32 and x86-64 instruction-set architectures that enables the creation of dynamic program analysis tools.
The tools created using Pin, called Pintools, can be used to perform program analysis on user space applications in Linux and Windows. As a dynamic binary instrumentation tool, instrumentation is performed at run time on the compiled binary files. Thus, it requires no recompiling of source code and can support instrumenting programs that dynamically generate code.
Installation and compilation of a project
Description
The below sections explain how to install pin and create a pintool (inscount0) based on the MyPinTool template and the cpp source code from inscount0.cpp.
Windows
Installation, configuration and compilation
- Install Microsoft Visual Studio 2010.
- Get pin (VC10) for Windows and copy all files to C:\pin:
- Open C:\pin\source\tools\MyPinTool\MyPinTool.vcxproj in Visual Studio and expand the Source Files section.
- Edit the MyPinTool.cpp file and replace its content with the source code of C:\pin\source\tools\ManualExamples\inscount0.cpp
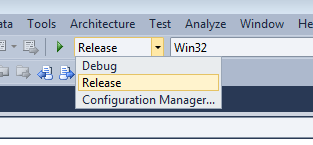
- Ensure you set Release as Solution Configuration option:
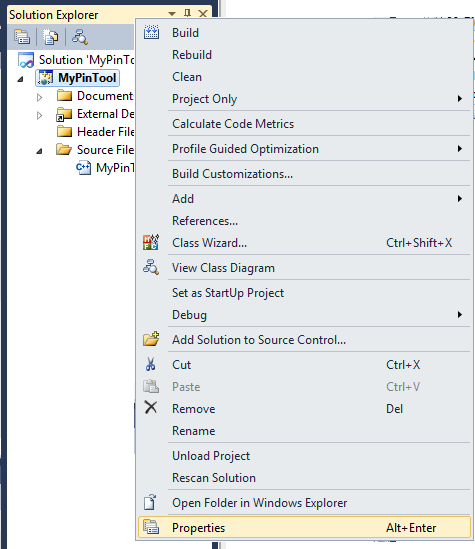
- Right click on MyPinTool and select Properties
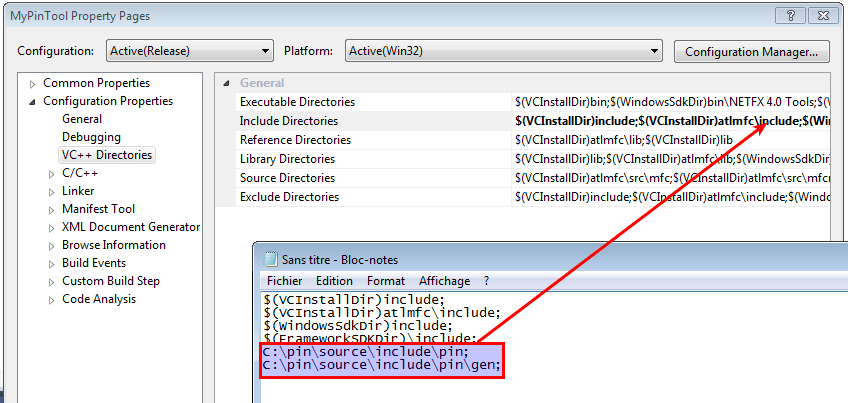
- Go to VC++ directories > Include Directories and add the following paths:
C:\pin\source\include\pin; C:\pin\source\include\pin\gen;
- Now you should be able to compile your project. Right click on MyPinTool and select Build. The output should be as follows and you should have a MyPinTool.dll file in C:\pin\source\tools\MyPinTool\
------ Build started: Project: MyPinTool, Configuration: Release Win32 ------
MyPinTool.cpp
Creating library C:\pin\source\tools\MyPinTool\Release\MyPinTool.lib and object C:\pin\source\tools\MyPinTool\Release\MyPinTool.exp
MyPinTool.vcxproj -> C:\pin\source\tools\MyPinTool\Release\MyPinTool.dll
========== Build: 1 succeeded, 0 failed, 0 up-to-date, 0 skipped ==========
Proof of Concept
Now suppose we have an executable that prompts for a password and we know the check is performed letter by letter. We can obviously guess that the number of instructions won't be the same if the probed letter is correct or incorrect. Here is how we can use the dll (renamed to incount0.dll) we have compiled with pin:
Providing an incorrect letter shows that the number of instructions is 32894:
C:\pin>pin.exe -t inscount0.dll -- \_malware\you_are_very_good_at_this.exe I have evolved since the first challenge. You have not. Bring it. Enter the password> a.......... You are failure C:\pin>more inscount.out Count 32894 C:\pin>pin.exe -t inscount0.dll -- \_malware\you_are_very_good_at_this.exe I have evolved since the first challenge. You have not. Bring it. Enter the password> b.......... You are failure C:\pin>more inscount.out Count 32894
But if the correct letter is provided, the number of instructions is not the same:
C:\pin>pin.exe -t inscount0.dll -- \_malware\you_are_very_good_at_this.exe I have evolved since the first challenge. You have not. Bring it. Enter the password> I.......... You are failure C:\pin>more inscount.out Count 32856
We can obviously automate this technique to brute force the password.
Linux
$ wget http://software.intel.com/sites/landingpage/pintool/downloads/pin-3.0-76991-gcc-linux.tar.gz $ tar xzvf pin-3.0-76991-gcc-linux.tar.gz $ cd source/tools/ManualExamples/
To build all examples in a directory:
$ cd source/tools/ManualExamples $ make all
To build and run a specific example (e.g., inscount0):
$ cd source/tools/ManualExamples $ make dir inscount0.test
To build a specific example without running it (e.g., inscount0):
$ cd source/tools/ManualExamples $ make dir obj-intel64/inscount0.so
This applies to the Intel(R) 64 architecture. For the IA-32 architecture, use "obj-ia32" instead of "obj-intel64":
$ cd source/tools/ManualExamples $ make dir obj-ia32/inscount0.so
To compile for a 32bit architecture, use the following instead:
$ make obj-ia32/inscount0.so TARGET=ia32
Comments
Keywords: pin pintools inscount0