SensePost-Yeti
Description
Yeti, developed by SensePost, enables to process requests from a given domain name. In the current release, the features are:
- Domain discovery (TLD expansion)
- Forward lookup brute forcing
- Reverse lookups
- Bing searching (IP: and SITE: searches)
- SSL Certificate scraping
- Web Spider
- Exporting results to XLS format
Installation and configuration
Prerequisites
First install Java and Nmap.
Installation
$ cd /data/src/ $ wget http://www.sensepost.com/cms/resources/labs/tools/misc/jyeti-dist.tar.bz2 $ mkdir -p /pentest/enumeration/www/ $ tar -C /pentest/enumeration/www/ -xjvf jyeti-dist.tar.bz2
Configuration
Start Yeti
$ cd /pentest/enumeration/www/jyeti-dist/ $ java -jar JYeti.jar
You should be presented with a similar screen:
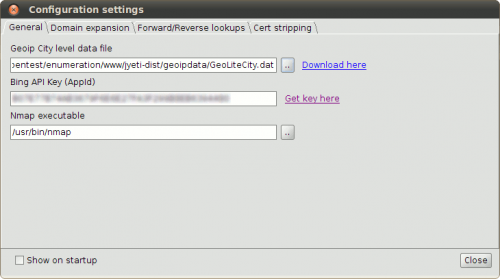
General
This tab enables to download and specify the path to following stuff:
- GeoIP database
- Bing API key (registration needed)
- Nmap executable: /usr/bin/nmap (default path)
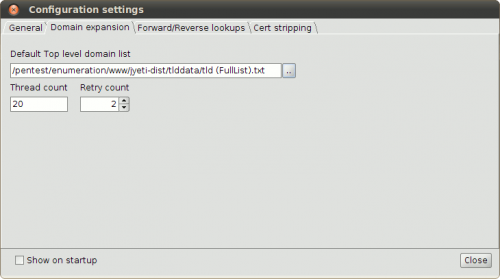
Domain expansion
This tab enables to specify the path to the TLD list file, initially located in the tlddata/ directory of your installation.
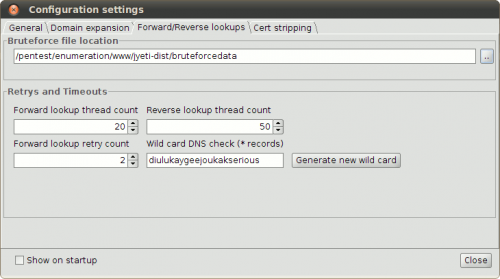
Forward/Reverse lookups
The installation comes with a dictionary containing a list of directories/files for brute forcing operations.
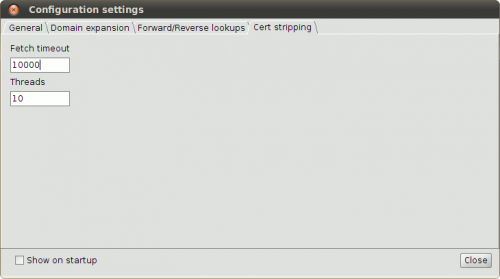
Cert stripping
Usage
Start Yeti
$ java -jar JYeti.jar
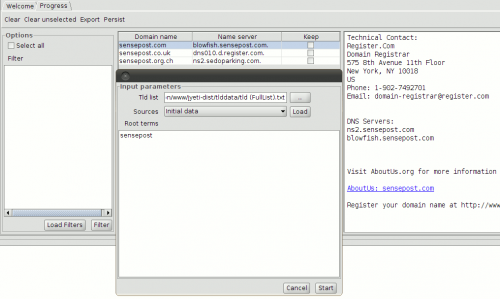
Domain Expand
This feature will look for valid domains from a provided root term (e.g. sensepost), by requesting a TLD file (initially in tlddata/tld (FullList).txt).
. .med.ht .sch.zm .idv.tw .gov.tn .nsw.au .gov.to .wy.us .name.et ...
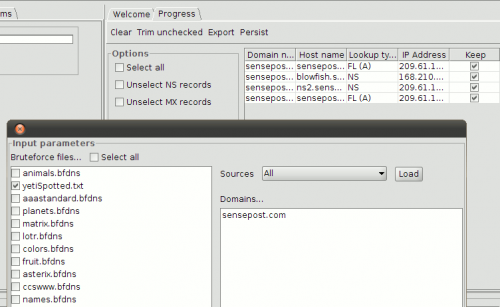
Forward Lookup
Based on a list of words grouped by themes (colors, animals, ...), this feature enables to bruteforce the discovery of valid hosts from a domain name. For each entry, it displays the type of record (NS, MX, A)
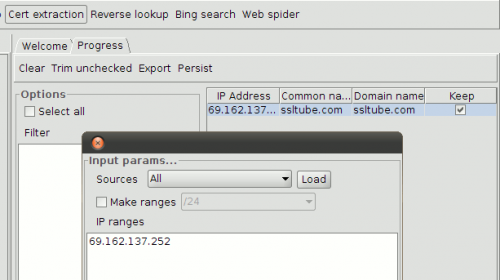
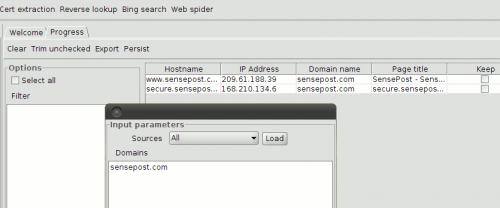
Cert Extraction
This feature extracts the information from certificates (https).
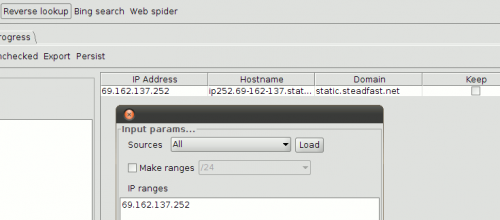
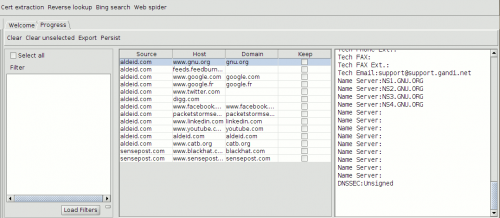
Reverse Lookup
Do a reverse lookup of a group of IP addresses:
Bing Search
Uses the Bing API to request Bing search engine from a given domain or IP address.
Web Spider
This feature parses a page and returns all domains contained in that page: