Support-apple-com-fr-retail-ipad-verification2013-personalsetup-dalatgap-com
Description
I'm always curious about phishing campaigns... This one is about fake Apple emails asking sensitive information (banking and personal) to complete their inventory...
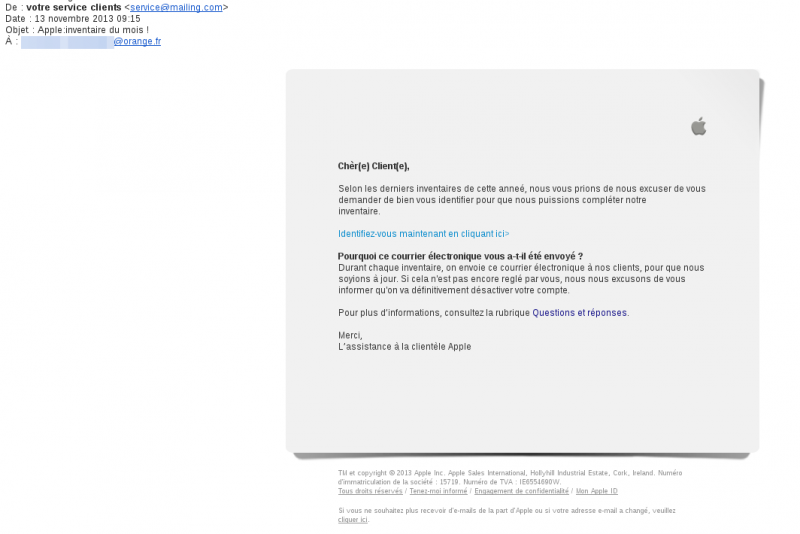
What we have from the initial email:
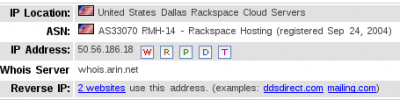
- It is sent from [email protected]
- the link points to http://www.cossuauto.nl/config.php
Redirection to the phishing website
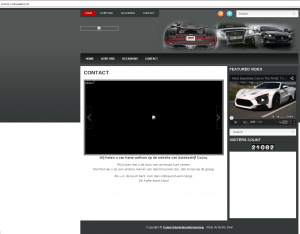
The website itself (www.cossuauto.nl) seems legtimate and related to cars. Attackers have probably found a vulnerability on the website and have left a config.php file on it to perform the redirection to their phishing website:
$ nc www.cossuauto.nl 80 GET /config.php HTTP/1.1 Host: www.cossuauto.nl HTTP/1.1 200 OK Vary: Accept-Encoding Content-Type: text/html Server: PCX/No-Cache Transfer-Encoding: chunked Date: Wed, 13 Nov 2013 12:29:37 GMT Age: 0 Connection: keep-alive X-Cache-Hit: No X-Cache: 1615577306 007f <META HTTP-EQUIV="Refresh" CONTENT="0;URL=http://support.apple.com.fr.retail.ipad.verification2013.personalsetup.dalatgap.com"> 0
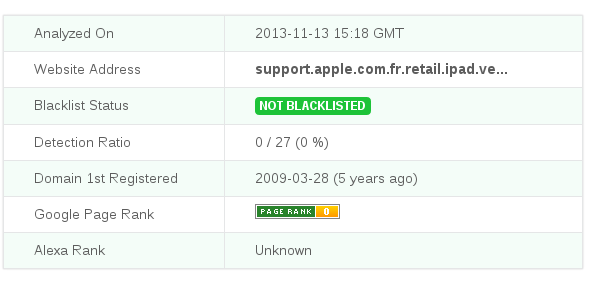
The domain (support.apple.com.fr.retail.ipad.verification2013.personalsetup.dalatgap.com) seems not to have a poor reputation:
...though identified as a phishing site by Google Chrome:
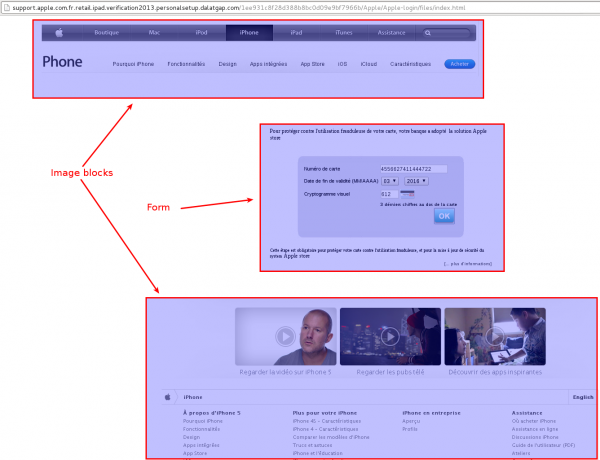
First form: credit card information
As for many phishing websites, the page is composed of images instead of real menus and links, and a form:
The webpage imports JQuery libraries to check user inputs:
<script src="images/jquery.js" type="text/javascript"></script> <script src="images/validate.js" type="text/javascript"></script>
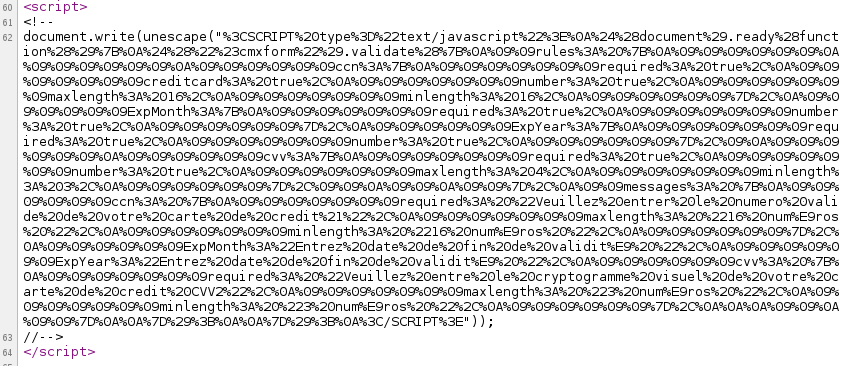
and obfuscates the part of the code that is the field description/controls:
Once deobfuscated, the code becomes:
//document.write (s) <SCRIPT type="text/javascript">
$(document).ready(function () {
$("#cmxform").validate({
rules: {
ccn: {
required: true,
creditcard: true,
number: true,
maxlength: 16,
minlength: 16,
},
ExpMonth: {
required: true,
number: true,
},
ExpYear: {
required: true,
number: true,
},
cvv: {
required: true,
number: true,
maxlength: 4,
minlength: 3,
},
},
messages: {
ccn: {
required: "Veuillez entrer le numero valide de votre carte de credit!",
maxlength: "16 numros ",
minlength: "16 numros ",
},
ExpMonth: "Entrez date de fin de validit ",
ExpYear: "Entrez date de fin de validit ",
cvv: {
required: "Veuillez entre le cryptogramme visuel de votre carte de credit CVV2",
maxlength: "3 numros ",
minlength: "3 numros ",
},
}
});
}); < /SCRIPT>
The form ensures that the credit card number is valid (based on http://jqueryvalidation.org/creditcard-method).
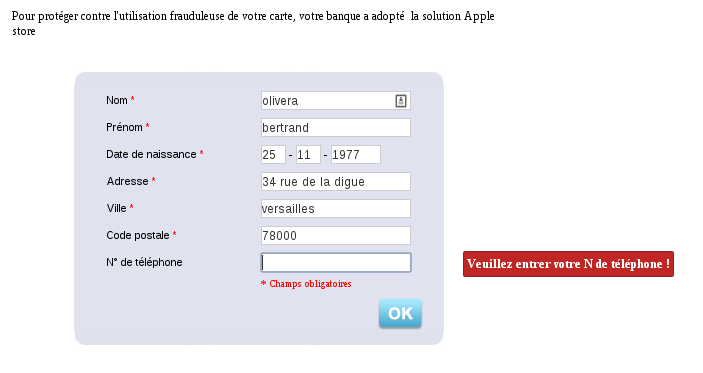
Second form: personal information
Once the first form is submitted, you're redirected to a second form, asking for personal information (last name, first name, birthdate, address, city, postal code, phone number).
- Notice that the phone number is required though indicated as an optional data in the form :)
- The form makes use of the same obfuscation mechanism as for the previous form
- There is a typo on the "code postale" field (there is no "e")
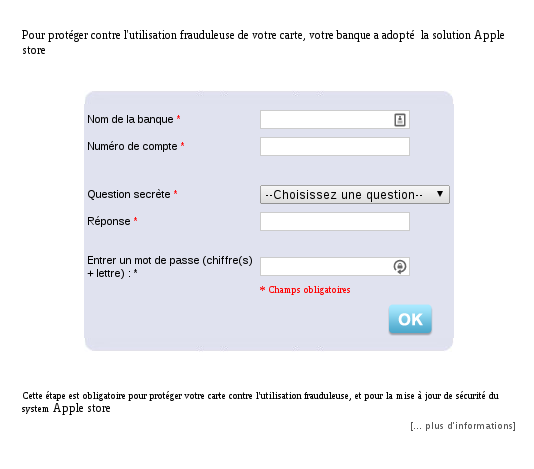
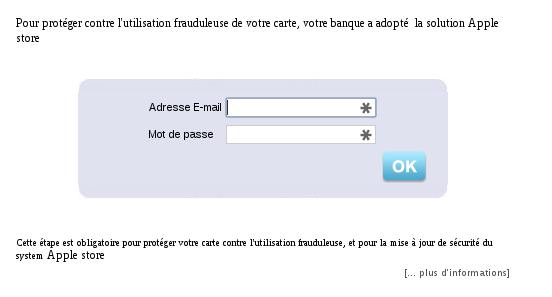
Third form: banking information
The third form asks for banking information and a password:
- This page does not obfuscate the form controls
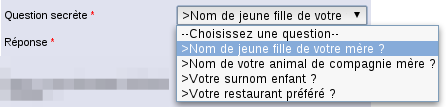
- There is a predefined list of 4 choices for the secret question:
Fourth form: email address and password
The last form is asking for the email address along with a password. It is not precised what the password should correspond to but I guess it should be your email password :)
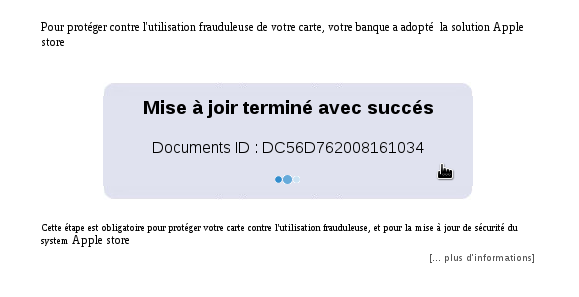
Confirmation and redirection to Apple's website
Once the previous form submitted, you're displayed a confirmation message (with a lot of typos) before being redirected to the Apple's website.