Watobo/Usage/Interceptor
Description
Data tampering is used to bypass controls that are executed on client side. in this lesson, you will learn how to use the Interceptor to tamper a request in order to divert the sending of a mail.
Example
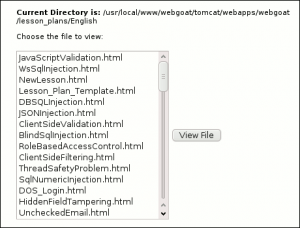
Our example will be based on WebGoat, Bypass a Path Based Access Control Scheme. In this example, there is a given list of files you can view by clicking on the "View File" button:
The list of files is taken from this directory: /usr/local/www/webgoat/tomcat/webapps/webgoat/lesson_plans/English/
We would like to access this file: /usr/local/www/webgoat/tomcat/webapps/webgoat/main.jsp
From the current directory, the relative path to our target is: ../../main.jsp. This is what we call a Directory Traversal attack.
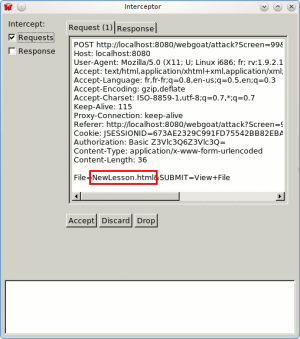
To do it with Watobo, open the interceptor mode (Tools > Interceptor) and check the "Requests" checkbox.
Point your browser to http://localhost:8080/webgoat/attack?Screen=99&menu=200, select a file from the list and click on the "View file" button. Go back to Watobo and analyze the request:
We notice that the filename is transmitted as a parameter. Transform the request by replacing the initial filename with "../../main.jsp" and click on the "Accept" button. You have bypassed the control executed on the client side!