ProcDOT
Description
ProcDOT is a tool developed by Christian Wojner from Cert.at. It processes Sysinternals Process Monitor (procmon) logfiles and PCAP logs (Windump, tcpdump) to generate a graph via the GraphViz suite. This graph visualizes any relevant activities (customizable) and can be interactively analyzed. It is very convenient for malware analysts.
Installation
Prerequisites
- Windump
- Process Monitor (procmon)
- CaptureBAT or any tool capable of capturing network traffic in a pcap file
- GraphViz: http://www.graphviz.org/pub/graphviz/stable/windows/graphviz-2.34.msi
ProcDOT
ProcDOT for Windows is available here: http://www.cert.at/static/downloads/software/procdot/procdot_1_0_31_windows.zip
Configuration of ProcDOT
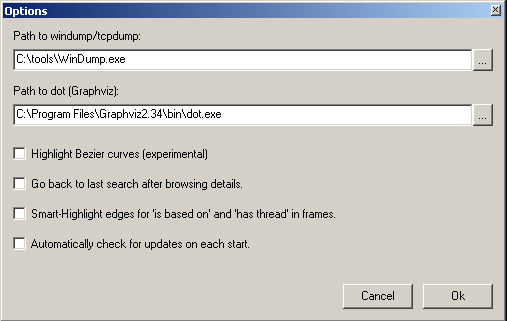
In order to be able to run ProcDOT, you will need to specify the path to WinDump and Graphviz.
Go to Edit > Options and complete the paths as follows:
Usage / Example
Capture (procmon + network traffic)
- First run Process Monitor (procmon) as well as CaptureBAT or any tool capable of capturing network traffic in a pcap file. For the sake of this example, we will run tcpdump with the -n -s0 options to have a copy of the network traffic.
- Run your malware sample
- Stop both Process Monitor (procmon) and CaptureBAT.
Procmon export
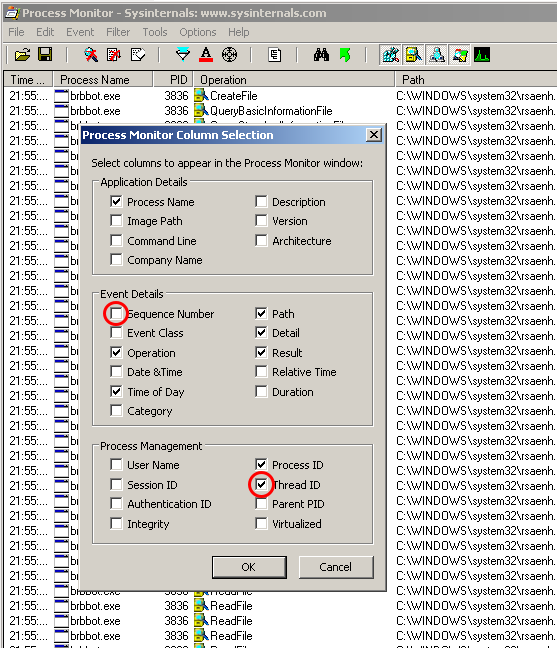
ProcDOT expects some columns in the export from procmon. In procmon, ensure that you:
- don't include the "Sequence Number" column
- include the "Thread ID" column
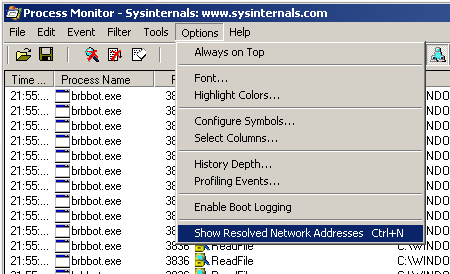
Also ensure that network addresses are not resolved:
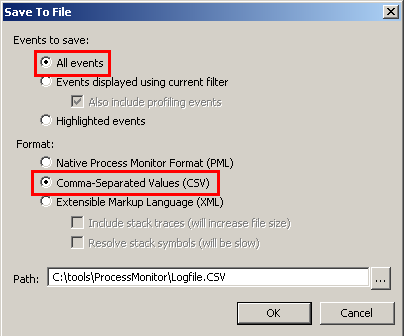
Then export (File > Save) the output under a CSV file as follows:
ProcDOT inputs
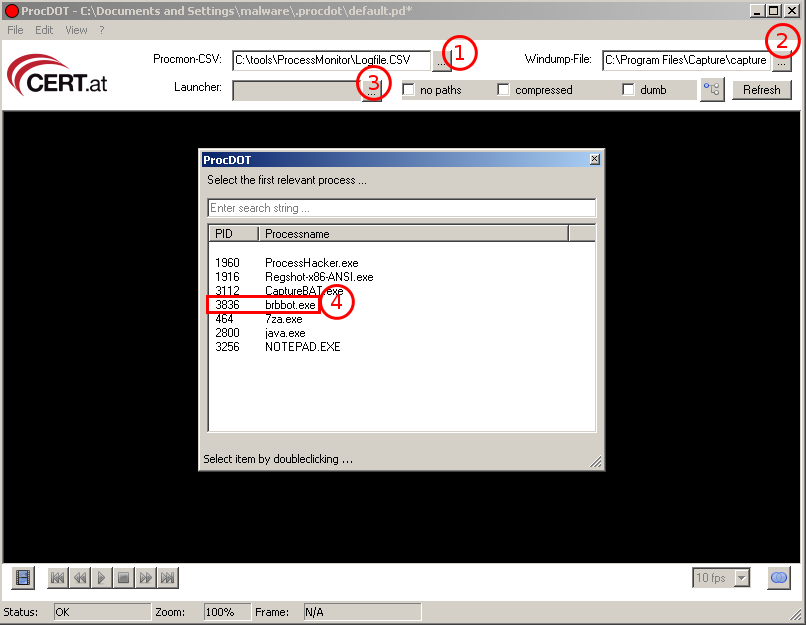
Now, it's time to start ProcDOT.
- Specify the path to your procmon CSV export...
- ...as well as your pcap file
- Click the Launcher browser button...
- ...and choose the process to analyze as entry point (double click on it)
Then optionnaly check the "no paths" (won't show full paths) and "compressed" (only includes some registry keys) boxes and click on the "Refresh" button.
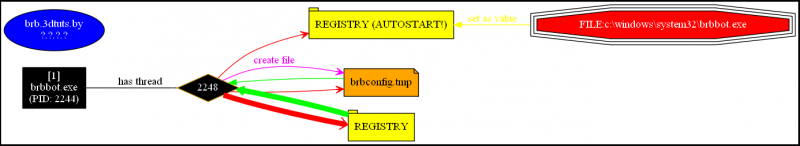
You should be able to display such a graph:
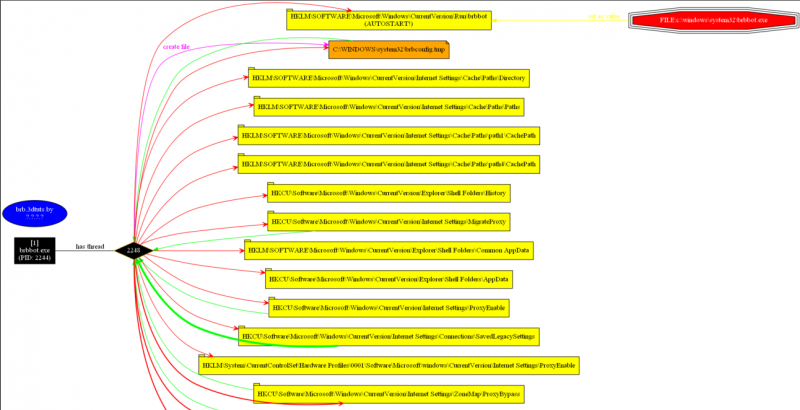
Here is how the graph would look like with paths ("no paths" unchecked) and uncompressed ("compressed" unchecked) options: