WackoPicko/Reflected-XSS-Behind-a-Flash-Form
| You are here: | Reflected XSS Behind a Flash Form
|
Description
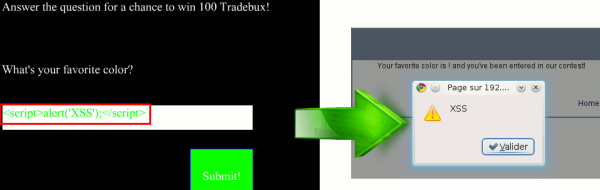
There is a XSS vulnerability on the page that displays your favorite color. The query parameter issued from the Flash form is not sanitized before being echoed to the user. The presence of the vulnerability can be tested by setting the query parameter to <script>alert(’xss’)</script>. When this string is reflected to the user, it will cause the browser to display an alert message. (Of course, an attacker would leverage the vulnerability to perform some malicious activity rather than alerting the victim.)
Click here for more information on XSS.
Proof of Concept
On the user’s home page there is a Flash form that asks the user for his/her favorite color. The resulting page is vulnerable to a reflected XSS attack, where the "value" parameter is echoed back to the user without being sanitized.
How to detect?
How to protect against it?
Code
Here is the portion of code that is unsanitized:
<div class="column prepend-1 span-24 first last">
<p>
Your favorite color is <?= $_GET['value'] ?>! and you've been entered in our contest!
</p>
</div>
The victim
Some wise advice:
- Don't trust links in your mails: Never click or double-check (analyze the real link behind the href) links you receive in your mails
The developer
A vulnerability is the result of the developer's mistake. Vulnerabilities come from:
- A lack of time during the development phase: Developers often have few days to develop an application. Under the pressure, mistakes and omissions are common.
- Poor testing phase: Often, testing phase focuses on the application's functionalities more than on security issues. Don't forget to cover this part.
- Lack of knowledge: Development is sometimes under the responsibility of beginners, which conducts to badly developed applications, especially for applications developed "from scratch". Use development frameworks that already implement security layers.