WackoPicko
Description
WackoPicko is a website written by Adam Doupé. It contains known and common vulnerabilities (XSS vulnerabilities, SQL injections, command-line injections, sessionID vulnerabilities, file inclusions, parameters manipulation, ...). It was first used for the paper Why Johnny Can't Pentest: An Analysis of Black-box Web Vulnerability Scanners.
WackoPicko has been developed as a *real* web application with following features:
- Authentication: WackoPicko provides personalized content to registered users.
- Upload Pictures: When a photo is uploaded to WackoPicko by a registered user, other users can comment on it, as well as purchase the right to a high-quality version.
- Comment On Pictures: Once a picture is uploaded into WackoPicko, all registered users can comment on the photo by filling out a form.
- Purchase Pictures: A registered user on WackoPicko can purchase the high-quality version of a picture.
- Search: The search feature offers the possibility to filter pictures by looking for strings in the tags of the images
- Guestbook: A guestbook page provides a way to receive feedback from all visitors to the WackoPicko web site.
- Admin Area: WackoPicko has a special area for administrators only, which enables the creation of new users.
This article will depict all of these vulnerabilities, ways to detect them and to protect against them.
Installation
Apache web server
First you will need:
- a valid Apache/PHP/MySQL installation.
- git: sudo apt-get install git-core

- I don't know whether WackoPicko has been intentionally written in that sense (a bug has been raised), but you will have to enable short_open_tag (set it to "On") in your php.ini file.
- If you install PHP from sources, notice that you won't be able to use Null byte attacks unless you use PHP<5.3.4. Indeed, PHP5.3.4+ deactivates usage of Null Byte in URLs.
- You will need the libjpeg library to be able to use the upload feature.
WackoPicko
Then, download WackoPicko:
$ cd /data/src/ $ git clone https://github.com/adamdoupe/WackoPicko.git
Install the MySQL database (it automatically creates a wackopicko MySQL user to access the database)
$ cd WackoPicko/ $ mysql -u root -p < current.sql
Install WackoPicko sources to the root of your web server:
$ mv website/* /var/www/ $ cd /var/www/
Give read/write privileges to the upload direcory:
$ chmod -R 777 upload/
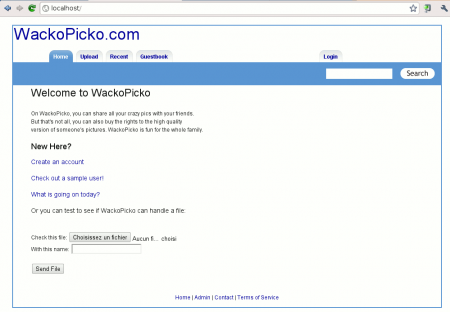
Test that the WackoPicko has been successfully installed by point your browser to this address:
http://localhost
You should be able to see the welcome page:
Valid credentials
| Priv | Username | Password |
|---|---|---|
| Standard | scanner1 | scanner1 |
| Standard | scanner2 | scanner2 |
| Standard | bryce | bryce |
| Admin | admin | admin |
| Admin | adamd | adamd |
Vulnerabilities
- Reflected XSS: In the search form, the query parameter is vulnerable.
- Stored XSS: The comment field is vulnerable to a persistent XSS attack.
- SessionID vulnerability: The session cookie value used for the administration authentication is based on a weak and guessable implementation (auto-incremental value).
- Stored SQL Injection: The first name field of the register users form contains a stored SQL injection which is then used unsanitized on the similar users page.
- Reflected SQL Injection: The username field is vulnerable.
- Directory Traversal: The tag field has a directory traversal vulnerability enabling a malicious users to overwrite any file the web server uses has access to.
- Multi-Step Stored XSS: The comment field is vulnerable to XSS, however must go through a preview form.
- Forceful Browsing: The user doesn't have to purchase the picture to see the high quality version.
- Command-line Injection: The password field is vulnerable to command line injections.
- File Inclusion: The /admin/index.php page is vulnerable to a file inclusion vulnerability, however you have to include %00 at the end.
- Parameter Manipulation: The userid parameter can be manipulated to see any user's page when you need to be logged in otherwise.
- Reflected XSS Behind JavaScript: The name parameter is vulnerable.
- Logic Flaw: A coupon can be applied multiple times reducing the price of an order to zero. The coupon in the initial data is SUPERYOU21.
- Reflected XSS Behind a Flash Form: The value parameter is vulnerable.
- Weak username/password: There is a default username/password combination of admin/admin.
Comments
Keywords: wackopicko