Watobo/Usage/Scans-types
Passive Scan
Description
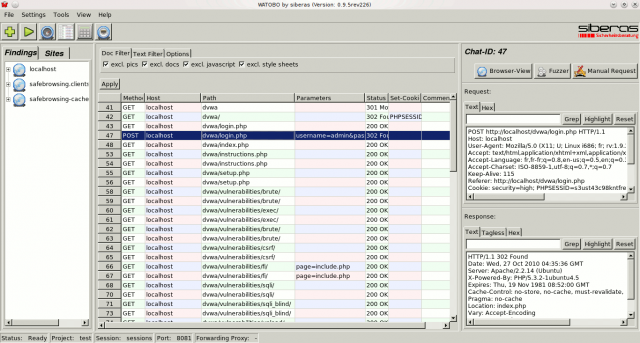
Passive scans consist of using the proxy functionality of Watobo while browsing the targeted application to discover vulnerabilities, tamper requests, and define a scope.
Example
Once you have initialized a new session, and parameterized Firefox's proxy, point to a web application of your choice (preferably vulnerable e.g. WebGoat, Damn Vulnerable Web App, Mutillidae, ...) and browse the pages.
You should be able to see the chats in Watobo:
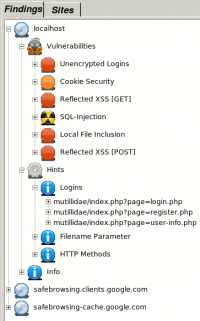
In the left panel, under the Findings tab, expand the section untitled "Vulnerabilities" to view discovered vulnerabilities. By expanding the tree, you will see the URLs of vulnerable pages. Click on one of them to load the request and response in the request/response panel.
Active Scan
Description
Active Scans are automated payloads/requests based on the results provided by a passive scan to discover, based on a selection made by the user. At the time of this writing, following tests can be done:
|
|
Example
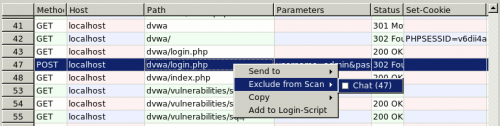
Exclusion of login pages
Since active scan is exploiting all chats, it is necessary to exclude login and logout pages from the scan in order to keep the session active. To do so, identify concerned chats from the chat table, right click on them and select "Exclude from scan > Chat (#)" from the contextual menu.
In the following example, we exclude these chats:
- Chat #47 because we transmit the credentials. The login page will nevertheless be analyzed on chat #43
- Chat #235 because we don't want to logout during the scan:
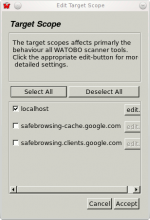
Target scope
Click on the Scan icon. It will popup a window enabling to select the target:
Eventually click on the "edit" button on the right of the target to specify filtering options. Then, click Next.
Payloads selection
Check all payloads you want to test by checking the checkboxes. Eventually expand the tree to select part of a test:
Then click Next.
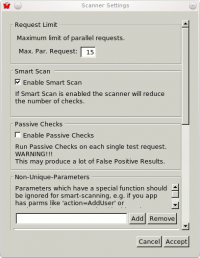
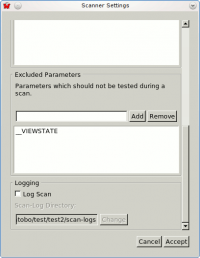
Scan settings
Eventually change scan settings:
Then click Start.
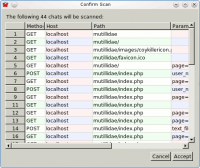
Confirm scan
Check that all chats are relevant for the scan, then click Accept.
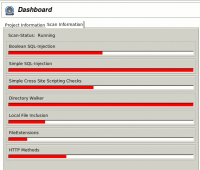
Launch the scan
It starts the scan. To see the progression of the scan, click on the dashboard icon or select "Dashboard" from Menu > View.
Once the scan is finished, come back to the chats view to see new discovered vulnerabilities: