The-FLARE-On-Challenge-01/Challenge-7
Jump to navigation
Jump to search
| You are here | Challenge 7
|
Description

INCOMPLETE SECTION OR ARTICLE
This section/article is being written and is therefore not complete.
Thank you for your comprehension.
Thank you for your comprehension.
Anti-reverse techniques & Internet connectivity checks
When we open the executable in IDA Pro, we can see that several functions are called, starting at offset 0x401B13. They are anti-reverse techniques and Internet connectivity checks.
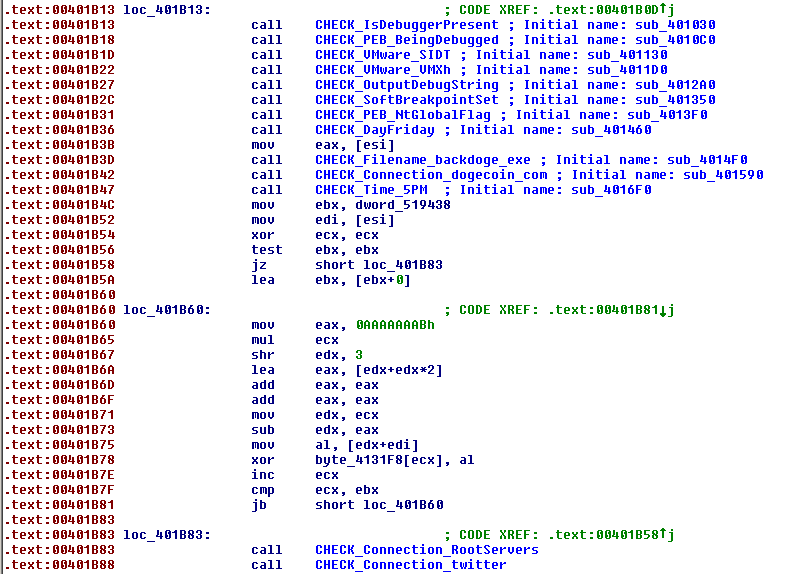
| Offset | Function | Category | Method |
|---|---|---|---|
| 0x401B13 | sub_401030 | Anti-Debug | IsDebuggerPresent() |
| 0x401B18 | sub_4010C0 | Anti-Debug | PEB.BeingDebugged |
| 0x401B1D | sub_401130 | Anti-VM | Check if running in VMware (SIDT_instruction) |
| 0x401B22 | sub_4011D0 | Anti-VM | Check if running in VMware (VMXh magic value) |
| 0x401B27 | sub_4012A0 | Anti-Debug | OutputDebugString |
| 0x401B2C | sub_401350 | Anti-Debug | Software breakpoint detection |
| 0x401B31 | sub_4013F0 | Anti-Debug | PEB.NtGlobalFlag |
| 0x401B36 | sub_401460 | Temporal | Check if Friday |
| 0x401B3D | sub_4014F0 | Filename-check | Check if name is backdoge.exe |
| 0x401B42 | sub_401590 | Internet Connectivity check | Check www.dogecoin.com |
| 0x401B47 | sub_4016F0 | Temporal | Check if 5pm |
| 0x401B83 | sub_4017A0 | Internet Connectivity check | Check e.root-servers.net |
| 0x401B88 | sub_4018A0 | Internet Connectivity check | Check https://twitter.com/FireEye/status/484033515538116608 |
Comments
Keywords: reverse-engineering challenge flare fireeye anti-reverse
Categories:
- CTF
- Digital-Forensics/Computer-Forensics
- Digital-Forensics/Computer-Forensics/Disassembler
- Digital-Forensics/Computer-Forensics/Anti-Reverse-Engineering
- Digital-Forensics/Computer-Forensics/Anti-Reverse-Engineering/Anti-Debug
- Digital-Forensics/Computer-Forensics/Anti-Reverse-Engineering/Anti-Debug/Debugger-Behavior-Detection/Temporal
- Digital-Forensics/Computer-Forensics/Anti-Reverse-Engineering/Anti-VM
- Digital-Forensics/Computer-Forensics/Anti-Reverse-Engineering/Anti-Debug/Check-Internet-Connectivity
- Reverse-Engineering/Challenges/flare-on-challenge
