Archives/2015
|
Solution to DaXXoR 101's KeygenMe #3 Sun, 6 Dec 2015 17:31:00 +0000 My solution to DaXXoR 101's KeygenMe #3. Patch and develop a keygen. Interesting technique of integrity checking. |
|
Solution to andrewl.us' Crackme #1 Sat, 5 Dec 2015 17:32:00 +0000 My solution to andrewl.us' Crackme #1. This is easy and great for beginners to learn crypto basics and python scripting in IDA Pro. |
|
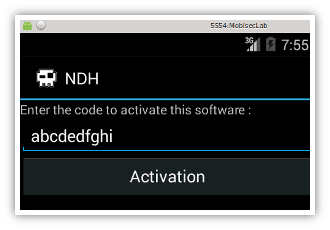
Solution to Profdraculare's keygenme228 Sat, 28 Sep 2015 20:44:00 +0000 My solution to Profdraculare's keygenme228 (crackmes.de). |
|
vik3790's Little Fish crackme Sat, 7 Nov 2015 15:13:00 +0000 My solution to vik3790's Little Fish crackme. A funny one! |
|
reZK2ll BeatME crackme Sun, 25 Oct 2015 17:46:00 +0000 A not so difficult crackme but some fun for the week-ends... |
|
Solution to FLARE-ON challenge 2015, challenge 10 Sat, 03 Sep 2015 18:10:00 +0000 My solution to FLARE-ON challenge 2015, level 10. |
|
Solution to FLARE-ON challenge 2015, challenge 7 Mon, 28 Sep 2015 21:26:00 +0000 My solution to FLARE-ON challenge 2015, level 7. |
|
Solution to FLARE-ON challenge 2015, challenge 9 Fri, 25 Sep 2015 17:36:00 +0000 My solution to FLARE-ON challenge 2015, level 9. |
|
Solution to FLARE-ON challenge 2015, challenge 8 Fri, 25 Sep 2015 17:32:00 +0000 My solution to FLARE-ON challenge 2015, level 8. |
|
Solution to FLARE-ON challenge 2015, challenge 5 Fri, 25 Sep 2015 17:27:00 +0000 My solution to FLARE-ON challenge 2015, level 5. |
|
Solution to FLARE-ON challenge 2015, challenge 4 Fri, 25 Sep 2015 17:23:00 +0000 My solution to FLARE-ON challenge 2015, level 4. |
|
Solution to FLARE-ON challenge 2015, challenge 3 Fri, 25 Sep 2015 17:16:00 +0000 My solution to FLARE-ON challenge 2015, level 3. |
|
Solution to FLARE-ON challenge 2015, challenge 2 Fri, 25 Sep 2015 17:12:00 +0000 My solution to FLARE-ON challenge 2015, level 2. |
|
Solution to FLARE-ON challenge 2015, challenge 1 Fri, 25 Sep 2015 17:01:00 +0000 My solution to FLARE-ON challenge 2015, level 1. |
|
Solution to DevAstatoR's What do I want crackme Thu, 23 Jul 2015 07:14:00 +0000 The objective of this crackme (http://crackmes.de/users/devastator/what_do_i_want/) is to find the value of 2 fields to reveal a password. This challenge is interesting because it requires some reverse engineering of the code itself to understand what is required. |
|
Shellshock Bash Vulnerability (CVE-2014-6271, CVE-2014-7169) Sun, 28 Sep 2014 10:52:00 +0000 Everything you should know about the Shellshock Bash Vulnerability (CVE-2014-6271 & CVE-2014-7169). |